Hackers exploited the tragic plane crash killing Poland’s president and other military and civil society leaders on April 10 by flooding search engine results with links to fake anti-virus software.
President Lech Kaczyinski and 91 other Polish dignitaries were killed when their Soviet-era model Typolev Tu-154 plane crashed in Russia while attempting to land in a heavy fog.
A Google search of “Tu-154” resulted in several pages of links that pointed to the same rogue antivirus software, ITBusiness.ca discovered Monday.
Gary Warner, a computer forensics expert at the University of Alabama at Birmingham conducted an analysis of the malware. Most antivirus scanners were unable to detect the malware masquerading as security software. The identity of the person who registered the sites is associated with more than 1,800 domains linked to similar scams.
“We went four pages deep on Google and 36 out of 40 results were malware,” Warner says. “That’s the kind of smack that gets people’s eyes to open up.”
Must Read: Gary Warner’s blog post about the attack.

Fake antivirus software often tricks a user into thinking they are infected with malware.
Clicking on the links brings the user to a page that appears to run a virus scan. It warns the user they are infected and asks for credit card information to buy fake antivirus software that will remove it. In reality, criminals steal the credit card information and load the user’s system with malware designed to steal even more personal information.
The malware, “packupdate_build6_195.exe” was detected by just eight out of 40 major anti-virus scanners in a test run at Virustotal.
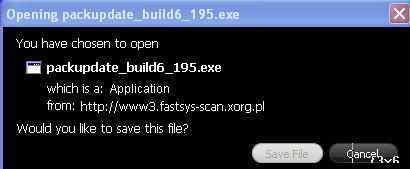
This program is a malware package.
The malware eventually changes Windows HOSTS file to redirect major search engines, including Google, Bing and Yahoo to a hacker network. Other online payment services and Google’s safebrowsing service are also redirected.
“Symantec, Sophos, McAfee, and Microsoft are not detecting this as malware at this time,” Warner notes. “In almost any corporation, there’s going to be a small number of people affected.”
Rogue security software, or scareware, is fraudulent security software that often convinces users to hand over payment information for bogus software after orchestrating a fake infection. Upon agreeing to buy the software, users are usually infected with malware that scours for more personal details that can be sold on the black market, according to a Symantec Corp. report released June 2009.
There are more than 250 distinct varieties of rogue security software on the Web and its purveyors are raking in the cash. Pushers for one piece of malware were paid an average of $23,000 per week.
“When you’re looking at pure signature-based detection, you have to have a more known threat” for it to work, says Marc Fossi, executive editor of Symantec’s Internet Security Threat Report. “That’s why we have reputation-based security.”
Rogue anti-virus attacks are prevalent and typically make use of popular news headlines to gain traction with search engines, he adds. Google and other search engines have been playing a cat-and-mouse game with hackers to stop malicious results from showing up.
Many of the infected sites under the “Tu-154” search are labelled with a warning – “This site may harm your computer.” But not all of them.
“They’re poisoning all of the top news headlines all of the time,” Warner says. “Especially when the term in the news headline doesn’t see a lot of traction normally.”
The hacker used a PHP script to comb through Google News and other similar sites to pull out headlines and build a malicious Web page for each of the top stories, he adds. Similar attacks were successful for events such as Michael Jackson’s death and the Beijing Olympics.
“When the stars align, his pages dominate Google and it’s extremely likely that someone is going to get infected by him,” Warner says.
The domains associated with the Tu-154 attack are registered to Garritt Kooken of the Netherlands. The e-mail address is listed as [email protected] and the phone number at +86-592257788, a China area code. The same registration information has been used for more than 1,800 domains conducting malicious activity.
Hackers use automated tools to register mass amounts of domains, Fossi says. “We’ll see them register a bunch of domains at one time and go live right after.”
The method allows the hackers to avoid getting blacklisted or shutdown. As soon as one domain is closed, another can be opened to serve the same malware.
Read Warner’s blog to get more information about the malware attack and details about how effective this specific hacker has been at infecting unsuspecting users.




