Experts are going hoarse telling organizations they have to build their cyber security strategies around doing the basics, including having an accurate inventory of everything on the network.
But if a survey sponsored by Tripwire is accurate not many are following even the top six of the 20 recommended Critical Security Controls set by the Center for Internet Security (CIS).
Among the survey’s findings:
- Only 11 per cent of respondents believe their organization tracks all hardware devices on their networks;
- Only 21 per cent say their organization tracks more 90 per cent of their software, while 56 per cent track less than 70 percent;
- A third of respondents said their organization doesn’t require changed default passwords, 41 per cent still don’t use multifactor authentication for accessing administrative accounts, and 43 per cent do not require unique passwords for each system;
- More than a third (38 per cent) said they still struggle to enforce configuration settings.
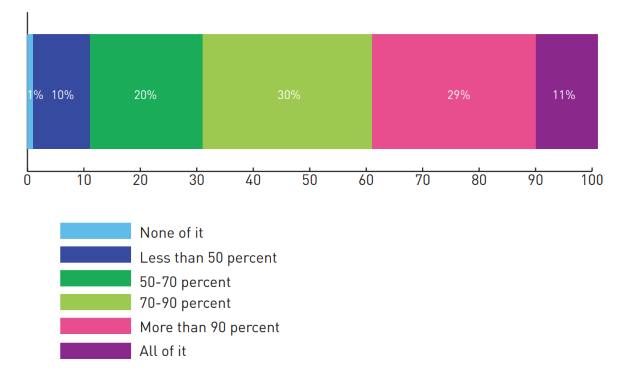
network do you have tracked in an asset inventory? (Tripwire graphic)
“These industry standards are one way to leverage the broader community, which is important with the resource constraints that most organizations experience,” Tim Erlin, Tripwire’s vice-president of product management and strategy, said in a statement. “It’s surprising that so many respondents aren’t using established frameworks to provide a baseline for measuring their security posture. It’s vital to get a clear picture of where you are so that you can plan a path forward.”
The survey was completed by 306 participants in Canada and the U.S. last month, all of whom are responsible for IT security at companies with more than 100 employees.
Many organizations still struggle to maintain the adequate visibility into their environments needed to address potential issues quickly, an analysis of the survey results found. “Results showed that organizations need to improve visibility into the devices and software on their networks, logs from critical systems, and configuration changes.”
The report, called The State of Cyber Hygiene, can be downloaded here. Registration is required.





