The words Windows and security have not always been compatible. In the past, Microsoft’s quest to make its operating system as easy to manage as possible for the “typical” user has often meant sacrificing adequate safeguards against intrusion and infection. Windows XP’s notorious vulnerability to network worms stands as a recent example; Microsoft shipped the operating system with a firewall but initially left it turned off by default.
For all its flaws, real and perceived, Vista marked a huge step forward in Windows security. Windows 7 has continued that improvement, adding several new features and enhancing many others — most obviously the User Account Control system, which proved so obnoxious in Vista that many users turned it off, leaving their systems vulnerable to intrusion in exchange for a less annoying experience. UAC has been revamped in Windows 7 to be less intrusive and more discerning about what constitutes a true threat, and therefore more effective.
Related stories
The pros and cons of Windows 7 security
Free Sophos tool blocks Windows attacks
Other Windows 7 security features are less apparent, especially those intended for businesses concerned with protecting not just one computer but an entire network. Among the most important new features are DirectAccess, a VPN replacement for computers on Windows networks; the Windows Biometric Framework, which standardizes the way fingerprints are used by scanners and biometric applications; and AppLocker, which improves on previous Windows versions’ Software Restriction Policies to limit which software can be run on a machine. Also key are BitLocker To Go, which extends the full-disk encryption of BitLocker to external hard drives, and a refined procedure for handling multiple firewall profiles so that the level of protection better matches the location from which a user connects to the Internet.
In typical Microsoft fashion, these features have been made available with little fanfare or guidance. Let’s take a look at each to see how they can help Windows shops secure their computers and networks.
Note that some of these features are available for all versions of Windows 7, while others require the Enterprise or Ultimate editions. What’s more, you won’t be able to fully implement some features until you’ve upgraded all your users to Windows 7, and at least one — DirectAccess — has back-end requirements that most companies don’t have in place yet. These features will, however, work side by side with older technologies for users who are still on earlier versions of Windows.
So even though you may not be able to take full advantage of all the new security features immediately, the time to start planning for them is now. We’ll start with the features that you can use right away and work our way up to those that require planning.
Multiple active firewall profiles
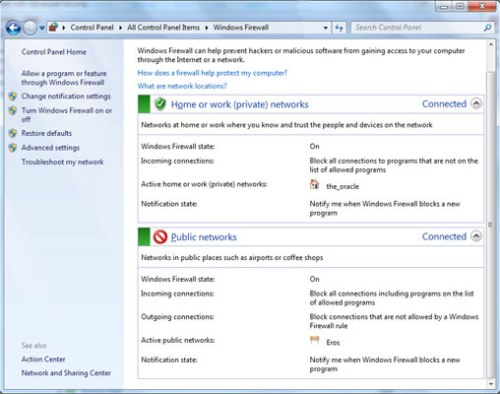
In Windows 7, each network connection can use its own specific firewall profile
Windows 7 offers a small but incredibly important improvement over Vista in its handling of firewall profiles. Vista allowed users to set up different firewall profiles for public, private and domain connections. A private network might be your home Wi-Fi network; aside from having the right WEP or WPA key, you don’t need any credentials to log in, but you trust it more than a public network like a coffee shop hot spot. A domain network requires authentication — a password, fingerprint, smart card or some combination of factors — to log in.
Each profile type has its own selection of applications and connections allowed through the firewall. For instance, in a home or small-business network marked Private, you might allow file and printer sharing, while on a network marked Public, you would likely disallow access to your files.
Vista’s firewall profiles worked well except when a computer was connected to multiple networks simultaneously, such as an Ethernet and a wireless network. In those cases, the system would default to the most restrictive profile. This could cause problems when, for example, connecting to a corporate VPN through a public Wi-Fi hot spot; Vista would recognize simultaneous connections to both a public and domain network and apply the public profile to both.
All versions of Windows 7 allow computers to keep several firewall profiles active at the same time, maintaining the access and functionality of the more trusted network while blocking access via the less trusted network. Since many remote access functions require less restrictive firewall settings, users can now work securely while remaining protected from threats outside of the corporate network.
Windows Biometric Framework
With fingerprint readers becoming more and more common on laptops, establishing a standard for the handling of biometric data has become important. Enter Windows Biometric Framework, a standardized method for storing fingerprint data and accessing it through a common API. Although most of the features of this subsystem are of interest only to developers, there are two important things that businesses should know.
First, while fingerprint scanners could formerly be used to log onto a computer but not to log onto a corporate domain (a corporate network or network subsection), the Windows Biometric Framework allows domain log-in.
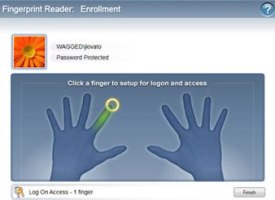
Windows Biometric Framework lets you easily store and manage prints for all of your fingers
Second, users can store up to 10 unique fingerprints, one for each finger. While most of us probably don’t expect to lose a finger anytime soon, having all 10 fingers enrolled in the system is a good precaution in case of lesser injuries. A cooking accident or a hand caught in a door can easily modify a finger enough that it won’t register correctly with a fingerprint reader, and you don’t want a user to be barred access to his computer while he heals.
Fingerprints are added using the Biometric Device applet, which appears in the Control Panel of any Windows 7 computer with a fingerprint scanner attached and from which you can enable computer and domain log-in. You must be logged in as an administrator to add or manage fingerprints on Windows 7.
BitLocker To Go
One of the most serious security threats facing today’s businesses is the loss of a mobile asset containing confidential corporate information. Windows Vista’s BitLocker began to address this problem by allowing business users to encrypt a laptop’s entire hard drive so that if it were lost or stolen, nobody could access the information stored on it. BitLocker To Go extends the same protection to even more easily lost external drives, including pocket-size hard drives and tiny flash drives.
Available in Windows 7 Enterprise and Ultimate editions, BitLocker To Go is simple to use: Right-click an external drive in Explorer and select “Turn on BitLocker” to open a wizard that will walk you through encrypting the drive, wait a while for the process to run, and you’re done. The wait depends on the speed of your computer and drives, but expect the initial encryption to take 20 minutes for a 2GB flash drive and up to a full workday for 500GB and larger external hard drives.
BitLocker To Go drives can be decrypted using a user-selected password and/or, in businesses that use them, a smart card for multifactor authentication.
Encrypted removable drives can be created only on Enterprise and Ultimate editions of Windows 7, but once you’ve created one, you can read from and write to it from any Windows 7 computer. You can also install a reader application on the encrypted drive that allows read-only access from Vista and XP computers.
Additional security can be implemented in corporate environments through the use of administrative policies that allow only BitLocker To Go drives to be written to, preventing users from storing data on nonsecure drives. Users of Windows Server can also keep a recovery password in escrow using Active Directory so that lost or forgotten passwords can be recovered.
AppLocker
Controlling what applications users can install or run is an effective way of maintaining the stability of users’ systems, preventing malware and protecting the integrity of the network from bandwidth-hungry applications like BitTorrent.
In previous versions of Windows, this was handled by the Software Restriction Policies feature. These policies could be applied to prevent specific software from running based on either its location in the file system or its failure to match a cryptographic hash of a known, trusted application.
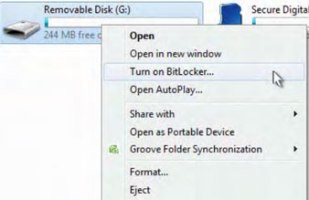
Encrypt removable drives, such as external hard drives and USB thumb drives, with Windows 7’s new BitLocker To Go
Software Restriction Policies could be a hassle to implement and maintain effectively. Some programs need to be installed outside of the typical path, necessitating new path rules to be generated. And hash-based policies offer powerful security but can fail whenever a program is updated. Any change to the program’s code — even a bug fix or security update — changes the hash and, if allowed, would prevent the program from running. Thus, IT managers had to maintain and update a cumbersome list of hash rules and override programs’ ability to update automatically.
AppLocker, available for Windows 7 Enterprise and Ultimate (as well as Windows Server 2008 R2), adds a new, more flexible method of controlling software: publisher rules. Publisher rules rely on information in a program’s signature certificate, which more and more applications have today.
This information is far more detailed than the file path or hash data, which lets admins create complex rules such as allowing software only from a particular publisher, with a particular name, with a specific file name and/or of a particular version to be run. For example, a rule could be created to allow anything from Adobe to be run, or only Photoshop, or only the current and future versions of Photoshop.
AppLocker rules can be applied to any executable, script, installer or system library, giving users enough latitude to, say, install needed software or updates without an administrative override, while still preventing them from using unauthorized software.
Furthermore, AppLocker rules can be written to apply to specific users or user groups; your accounting team and your graphic design team probably have very different software needs, but with AppLocker, only one set of policies is needed to provide each group with its own unique set of restrictions and allowances. AppLocker can even distinguish among users who share the same computer.
A real timesaver is the ability to automatically generate rules from a trusted reference computer. Policies can be exported and applied globally across the network using Windows’ Group Policy settings. (See Microsoft’s TechNet for a step-by-step guide to using AppLocker.)
It’s important to note that AppLocker rules apply only to users whose machines are running Windows 7 Enterprise or Ultimate editions. If some of your users have older Windows versions, you’ll need to keep Software Restriction Policies in place for them. As more users upgrade to Windows 7, you can phase out SRP and rely on AppLocker.
DirectAccess
Billed by Microsoft as a “next-generation” replacement for VPNs, DirectAccess allows Windows 7 Enterprise and Ultimate users to connect directly to Windows 2008 R2 and future servers. Whereas users generally have to initiate VPN connections, DirectAccess is completely transparent for end users: When the computer connects to the Internet, DirectAccess automatically creates a secure connection to the corporate network without any action on the user’s part, and automatically routes requests to the internal network through that connection.
DirectAccess offers improvements over traditional VPNs beyond the automatic connection. First of all, it uses IPsec and IPv6 Internet protocols to encrypt and route the connection from end to end. Where VPN encryption is stripped at the VPN server, DirectAccess can remain encrypted all the way to and from the application server inside the corporate network. (DirectAccess supports a number of other protocols to create tunnels for this traffic across networks that do not support IPv6 or IPsec yet.)
And because DirectAccess uses a standard Internet port for traffic, it easily traverses firewalls without any additional configuration, something VPN users often have trouble with.
Another benefit: Because the connection is created and maintained automatically, administrators can continuously manage and update DirectAccess-enabled computers, even when the user is not directly using corporate resources. Remote users tend to connect through a VPN only when they need access to network resources; depending on the worker, weeks may go by between VPN connections.
This means that VPN users must be quarantined, scanned and patched before they can be allowed access to the corporate network, a process that slows down the connection and limits worker productivity, as well as providing IT administrators with only small windows of time to manage their remote computers. With DirectAccess, computers are updated at the same time as the rest of the corporate network and can be monitored regardless of whether the user needs access to the corporate network.
Note, however, that it won’t be practical for most companies to move to DirectAccess right away. The system relies on an advanced network infrastructure — including Windows Server 2008 R2 and IPv6 — that many businesses have not yet rolled out or are incrementally upgrading to, so it may be several years before many companies have all the tools and technologies in place to move fully to DirectAccess. During the ramp-up phase, it can be run alongside a traditional VPN.
But it provides a glimpse into the future of networking — a secure, always-on connection to “home base” that allows remote employees to work as if they were sitting in the central office.
For businesses, Windows 7 allows a partnership of sorts to be established between the security-savvy IT department and the end user, letting employees get to work while security policies are applied and updated from the network. What all these features share is a commitment to ease of use that does not come at the expense of real security, showing a Microsoft that seems to have finally recognized that the two are not necessarily incompatible.
Logan Kugler is a frequent Computerworld contributor.
Source: Computerworld




