It’s no wonder the Conficker worm dominated computer security concerns in 2009 so far – the community was too busy battling against the deluge of end-user targeted attacks in 2008 to worry about the network-oriented vulnerability exploited by Conficker, say security experts.
Conficker, also known as Downadup, surfaced on the radars of security vendor Symantec Corp. last year when it exploited the Microsoft Windows Server Service RPC Handling Remote Code Execution vulnerability.
Though exploited near the end of the year, it was still the top vulnerability in Symantec’s Internet Security Threat Report for 2008.
The annual report was released today. Symantec is moving from a bi-annual format for the security report so it can get a better look at the overall trends, explains Marc Fossi, executive editor of the report. Next year’s report will likely be filled with information about the Conficker worm.
“It is a high profile attack but we didn’t start to see a lot of activity fromm it until January and February,” he says. In 2008, “everyone was so busy securing the endpoints against Web-based stuff they didn’t keep up defences against network worms.”
Since 2004, security researchers have seen a trend in Trojans that target end users favoured over network-focused worms.
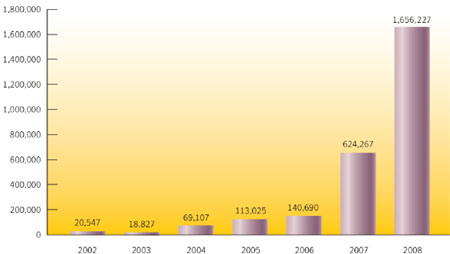
Overall, 2008 was a continuation of that trend as cybercriminals continued to attempt the spread of malware to be used in an effort to collect confidential information. The hackers created more than 1.6 million new threats in 2008 – a staggering amount considering that 2007 saw the creation of 624,267 new threats and 2006 saw just 140,690.
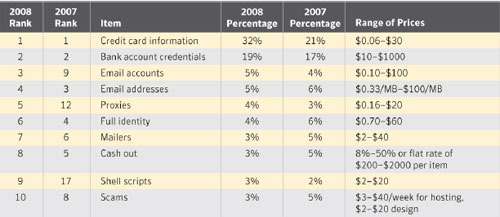
Once they have credit card numbers or bank account information, they go to sell the information on the underground economy.
Credit card information is the most-advertised stolen information on the black market (32 per cent) and bank account credentials are the second-most (19 per cent), according to Symantec. A single credit card number can be sold from as low as 6 cents to as much as $30.
Of the 245 million malicious programs were seen across the globe each month on average by Symantec, 90 per cent designed to steal confidential information. This was most commonly accomplished by allowing remote access, and then by exporting user data.
“Your confidential information has value, especially with the way the economy is right now. That’s what all these attackers are after,” Fossi says. “The underground economy is recession proof and we aren’t. When things are tight, the last thing you need is money to go missing from your bank account.”
Most people are shocked to learn how easy personal information can be scrapped off the Web and then the cheap price it is sold for on the black market, says Candice Low, a research analyst with London, Ont.-based Info-Tech Research Group.
“If more people learn and understand how this data is stolen, the better equipped they will be to prevent these thefts,” she says. “Stolen financial data is sold for pennies on the black market.”
Most vulnerabilities exploited by attackers have already been patched by software companies, Fossi says. But many computer users neglect to install patches and remain vulnerable to the attacks.
For example, the top vulnerability attacked in 2008 was an Internet Explorer glitch that Microsoft fixed in 2003.
Trends in 2008 saw the increasing organizational sophistication of hackers intent on conducting profitable cybercrime. It’s a far cry from a time when hackers such as Mafiaboy defaced Web sites for bragging rights. Now it’s about making money.
To sidestep the law, attackers are moving operations out of developed countries with established Internet security policies and into emerging Internet infrastructures. For example, the U.S. remains the top originator of spam in 2008, accounting for 25 per cent of the overall spam volume.
But that’s down from 45 per cent the previous year. Meanwhile, Turkey saw its share rise to five per cent from one per cent, and Brazil doubled to four per cent.
“That’s where the attackers are setting up their spam relays now,” Fossi says. “These guys are almost becoming like pseudo-corporations.”
These cybercrime outfits even hire workers to work full-time towards making scams successful, he adds.
Canada can take some comfort in knowing that it is not a major origin of cybercrime. It has dropped four spots on the world rankings for malicious activity since 2007. Only about three per cent of attacks originate from Canadian servers, and less than two per cent of spam originates from Canada.
Toronto is the city most infected by botnets, or automated spamming programs, at 12 per cent of the country’s bots. But that is still less than one per cent of the number of bots infecting computers on a global scale, and placed 58th on the world ranking list.




