The good news is that traditional techniques used by cyber criminals to cover their tracks are becoming less effective.
The bad news – security researchers have recently discovered the emergence of combined attacks that punch through company firewalls and anti-virus tools.
Attackers are now using both JavaScript and Adobe’s ActionScript languages to slip pass traditional defenses, according to M86 Security, an Orange, Calif-based real-time threat protection firm. M86 Security Labs analyzes spam, phishing and malware activities by studying millions of distinct e-mail messages and malware reports each day. The report covers January to June of this year.
Related stories
Cyber Security as a Service for Canadian Small Business
‘Canadian Pharmacy’ spam – a nightmare for legit firms
Familiar hacker methods such as spam bots and dynamic code obfuscation have waned in effectiveness, according to Bradley Anstis, vice-president of technology strategy at M86. “However, during the first half of 2010 we’ve seen the emergence of combined attacks that outsmart even the latest Internet security mechanisms,” he said.
Attackers, Anstis said, have begun splitting malicious code between ActionScript which is built into Adobe Flash and JavaScript components on Web pages. By doing this, cyber criminals are able to prevent current security tools from detecting attacks.
Of the 15 most exploited vulnerabilities observed by M86, four involved Adobe Reader and five involved Internet Explorer.
Wake up Call
“This is a wake up call especially for small and medium sized businesses (SMBs) to get their defenses up to snuff,” said Anstis.
He said a lot of smaller organizations are still relying on anti-virus and URL filtering tools, which he characterized as “reactive controls”.
These tools are not effective against the new onslaught of malware which latch themselves onto legitimate Web sites that are not blocked by signature-based security systems. “While old mass-mailers such as Netsky still exist, their numbers have dwindled. Today the biggest concerns arise from malicious attachments and blended threats where spam contains a link to a malicious Web page,” said Anstis.
He said the report indicates that most exploits reported more than a year ago have already been addressed by software vendors. “This highlights the need for SMBs to keep up-to-date with patches and the latest software versions in order to gain better protection… [Next Page]
The M86 executive also said SMBs can no longer count on their size to obscure themselves from attacks. “SMBs are no longer hidden from cyber-criminals. In many instances, SMBs are targeted as low hanging fruits.”
Canadian Pharma tops spam campaigns
The M86 report also indicated that botnet operators are raking in money by exploiting public trust in Canadian pharmaceuticals.
Anstis explained that spammers typically enroll in “affiliate programs” that pay them for promoting products via spamming unsuspecting Internet users. Botnet operators are paid commission on each successful sale.
The affiliate programs can provide many resources to affiliate members. Depending on the program these could include pre-registered domains, Web branding pages, undetectable executable codes and even daily statistics on how many users are visiting these spam sites.
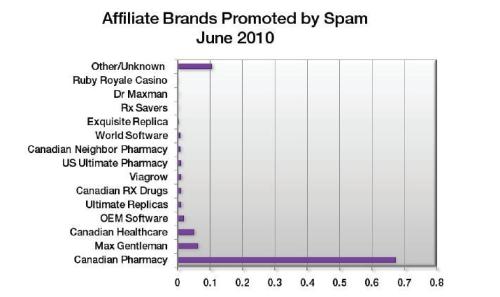
Some affiliate programs have several different brands from which members can chose from, but the most popular brand appears to be one called “Canadian Pharmacy”.
The M86 report indicated that as much as 67 per cent of drug-related spam can be traced to the Canadian Pharmacy brand. Brands that have the word Canadian in them are included in the top 10 affiliate programs, said Anstis.
“The Canadian name conveys a sense of security among consumers. Online buyers are more likely to trust companies when they see that it’s Canadian,” he said.
But the actual companies advertising the pharmaceuticals are not located in Canada. Most spam for this category is sent from computers outside of Canada as well.
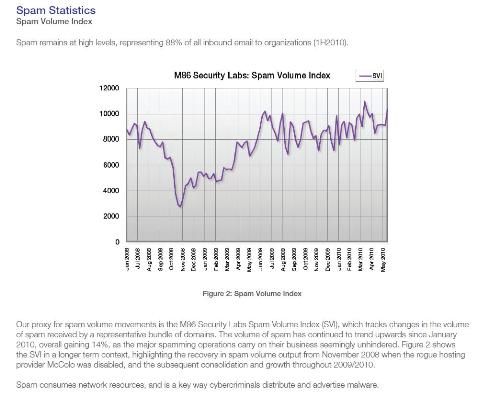
Overall spam output continues to remain extremely high showing a gain of no less than 14 per cent since January this year. The report said just five botnets account for 75 per cent of the spam.
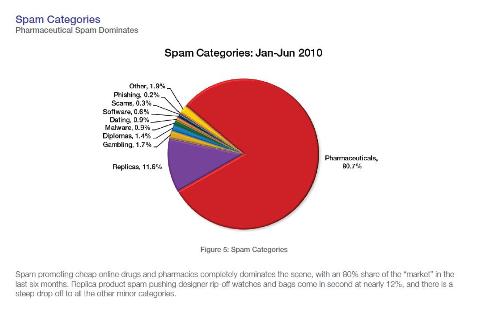
Spam promoting pharmaceuticals constitute about 80 per cent of all spam.
M86’s findings echo those of Symantec Hosted Services, which also reports that “Canadian Pharmacy style spam” is on the rise.
Symantec researchers found that the spike in spam volumes were driven by a Canadian Pharmacy-style spam and that the Grum and Rustok botnets were generating the surge,” according Matt Sergeant is a Senior Anti-Spam Technologist with Symantec Hosted Services.
He said the spam rate in Canada was 88 per cent with one in every 364.8 e-mails containing malware. An average of 4,998 new Web sites per day was identified as harboring malware or other unwanted… [Next Page]
How SMBs can protect themselves
Small businesses that have limited budgets or security resources are not totally helpless, against spammers, according to Anstis of M86.
He said SMBs can employ these simple and practical security best practices that will limit their exposure to online threats:
- Be selective about registering your e-mail address to limit exposure to phishing attacks. Consider creating a separate e-mail account which you can use when signing up for mailing lists.
- Delete spam immediately and unsubscribe to even legitimate mailing list that you no longer need. Never buy products from spam messages.
- Avoid clicking on suspicious email links or instant messages. Many spammers also create bogus sites that appear to be Web pages of legitimate firms.
- Deploy an anti-spam tool across the whole organization. Remember that signature-based anti-virus solutions are no longer adequate.
- Do not fill out online forms that ask for personal or financial information and passwords.
Get more information about spam protection from ITBusiness.ca
Canada introduces anti-spam law as spam URLs become pervasive
Free anti-spam and malware tool for Facebook
New Brunswick is ‘spam capital’ of Canada
Nestor Arellano is a Senior Writer at ITBusiness.ca. Follow him on Twitter, read his blog, and join the IT Business Facebook Page.