Yes, the truth is out there. But they don’t want you to know about it.
Who’s “they”? It could be Google or product manufacturers, your boss or your wireless carrier, Hollywood or Uncle Sam.
What don’t they want you to know? That your cell phone, your Webcam, and your employer may be spying on you. That you’re probably paying too much for printer ink, and that your wicked-cool subsidized handset will cost you way more over time than an unsubsidized one. That your PC may be coated with toxic flame retardants. And that’s just for starters.
Related stories
5 ways to monitor your employees legally and ethically
Use employee monitoring tools with caution, say Canadian experts
Don’t despair. For every dirty little secret revealed herein, we describe a fix or a way to work around it (if any exists). You don’t have to be a victim, if you know what to do.
Just remember: You’ve been warned.
Your ISP Is a Copyright Cop
The RIAA and the MPAA may have a new ally. The next people who bust you for illegally swapping music and movies could be the folks you pay for Internet access.
The recording and film industries are seeking to manipulate upcoming net neutrality legislation to allow ISPs to scan the bits passing through their networks and to block any that may violate copyrights–similar to Comcast’s notorious attempts to throttle BitTorrent connections in 2007. The Federal Communications Commission’s recommended rule changes already contain an exception for “reasonable network management,” which could include sniffing for copyrighted content, says Jennifer Granick, civil liberties director for the Electronic Frontier Foundation.
Meanwhile, according to leaked reports, the international Anti-Counterfeiting Trade Agreement (ACTA) now being negotiated in private sessions contains provisions requiring ISPs to police their own networks for copyright scofflaws. Critics of the proposed treaty fear that copyright holders will insert a “three-strikes” policy, under which users could have their Internet access revoked if they’re caught exchanging copyrighted content more than twice.
“It’s dangerous giving so much power to copyright claims,” says Wendy Seltzer, project leader for the Chilling Effects Clearinghouse and a Fellow at Harvard’s Berkman Center for Internet & Society. “Imagine someone telling you, ‘If you violate our copyrights, we can terminate your Net connection, not just your blog.'”
With such a powerful new partner playing the role of both investigator and enforcer, might copyright holders be emboldened to pursue more consumers suspected of violating copyrights? And what protections will consumers have against false claims of infringement?
The Fix: Contact your congressional representatives and tell them that you oppose net neutrality loopholes for content filtering. Support organizations such as Chilling Effects, the EFF, and Public Knowledge, which fight laws that turn ISPs into Hollywood’s hired guns.
Cell Phones Don’t Crash Airplanes
The Federal Communications Commission and the Federal Aviation Administration have each recommended that airlines not allow passengers to use cell phones during commercial flights. The FAA fears that the RF signal emitted by devices using the 800MHz spectrum band might interfere with the navigation systems of the plane, specifically GPS instrumentation. Yet there is no documented case of an air accident or serious malfunction caused by a cell phone’s interfering with a plane’s navigation system.
The FCC’s concern is that wireless networks on the ground might be disrupted by the cell phones flying overhead. As a plane flies over a wireless cell tower on the ground, the FCC believes, the cell site will detect all the cell phones operating inside the plane and go to work registering those devices to operate on the network. But by the time the tower registers and connects all those mobile phones passing overhead, the plane will have passed into the range of the next cell tower on its route. This uses up system resources and could hurt network performance for connected phones on the ground.
But some experts believe that this worry is outdated. “Color me highly skeptical that this is a real problem with modern systems,” says Ken Biba, CTO of Novarum, a wireless consulting and engineering group. “Modern digital phones actually use lower power, and, further, the cell towers have very directional antennas designed for covering the surface of the earth [not the air above].”
The Fix: There isn’t much you can do. Actually, the FCC and the FAA are doing us a big favor here. They’re delivering us from having to fly with people jabbering away on their cell phones from takeoff to landing.
‘Private’ or ‘Incognito’ Browsing…Isn’t
These days, most major Web browsers offer “private” or “incognito” browsing (known colloquially as “porn mode”). But all the feature really does is tell your browser not to record the sites you’ve looked at, the search terms you’ve used, or the cookies deposited during that session.
If the sites you visit record your IP address (and many do), that information is available to any interested party that has the legal right to request it–a group that can include divorce attorneys and law enforcement. Recording visitors’ IP addresses is a trivial task–you can add to any blog a free widget that accomplishes the same thing–so you should assume that the sites you visit do so.
Of course, your Internet service provider assigned you the IP address in the first place, so it can track you anywhere you go online, if it so chooses. In fact, the FBI wants ISPs to store your surfing histories for at least two years. So far, major ISPs have resisted this push, in part because the storage and record-keeping requirements would be enormous. What information ISPs retain, how long they keep it, and how public they are about it vary from provider to provider–most won’t talk about it. (One exception is Cox Communications, which says that it retains IP address logs for six months.) So while your spouse may not know what you’ve been up to online, the feds might.
The Fix: If you really want to browse off the record, use a proxy service, like Anonymizer or Tor, that obscures your IP address as you surf.
You’re Spending Too Much on Printer Ink
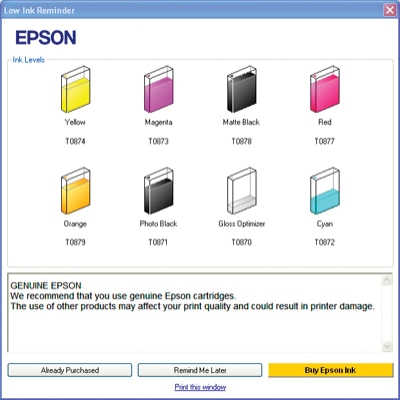
If there was ever a business built around scare tactics, it’s the business of selling inkjet printers. Try using a refurbished or refilled cartridge, and the printer maker may warn you that you’re voiding your service warranty, putting your printer at risk of damage, or possibly ruining your printouts.
Top 10 free or cheap downloads to unlock your printer’s potential
Nonsense, says Bill McKenney, CEO of InkTec Zone, which sells equipment for refilling inkjet cartridges to retailers such as Wal-Mart International.
“You won’t void the warranty and you won’t hurt your printer,” says McKenney. “A bad refill job may leak ink inside your machine. Otherwise you’ll be fine. And the savings are so significant, there’s almost no reason not to do it.”
In fact, PCWorld’s own lab testing shows that while prints made with third-party, refurbished, or refilled ink cartridges aren’t always as good as those made with the printer manufacturer’s ink, the cartridges are safe to use in your printer.
The exceptions are so-called prebate cartridges, sold at a slight discount, that contain a chip preventing their being refilled (which should be clearly labeled as one-use-only products).
The Fix: Buying a refurbished cartridge can save you 10 to 20 percent off the price of a new one. Getting refills bumps that savings to 50 per cent or more.
The drawbacks are that you may not get quite as much ink with a refill (the amount is usually at least 95 per cent, McKenney says), archival prints may not maintain their color quality for as long, and you can refill each cartridge only three to eight times before you’ll have to recycle it and get a new one.
End User License Agreements May Not Be Enforceable
It doesn’t take much effort to sign an end user license agreement: Rip open a software package, or tick a box on a Website, and you’re legally bound. But your obligations depend a lot on where you live, says Jonathan Ezor, director of the Institute for Business, Law & Technology at the Touro Law Center on Long Island.
“EULAs are contracts, and contract law is state law,” says Ezor. “It’s governed by the state where you live or where the company is based.” For example, courts in the Third Circuit Court of Appeals (Delaware, New Jersey, and Pennsylvania) and the Fifth Circuit Court of Appeals (Louisiana, Mississippi, Texas) have found certain types of EULAs invalid.
Other factors include whether the agreement contains unenforceable restrictions, whether it gives consumers sufficient choice, and what method it provides for users to indicate agreement, Ezor adds.
The odds of your going to court over a EULA, however, are slight. The real issue is how companies enforce them, Ezor says.
“What companies really don’t want you to know is how easy it is for them to turn things off or erase them,” he adds. “Think of what happened last year with the Orwell books that Amazon just erased from people’s Kindles.”
The Fix: Read the EULA. Does the software “phone home” to verify that you’re using the product as its creator intended–and, if you’re not, does it have the ability to disable the program remotely? If it doesn’t, you’re probably free to do as your conscience allows.
The Cyberwar Is Heating Up (and Uncle Sam Is Losing)
We may be at war on the ground in Afghanistan, but bigger battles are being waged beneath the noses of most Americans. For the past several years, U.S. government computer networks have been under siege from foreign adversaries. What the people in charge don’t want you to know is that it could have been prevented.
Attacks on Department of Defense computer systems jumped 60 percent in 2009, according to a congressional committee. Last July, a botnet originating in North Korea launched a sustained DDOS attack on several U.S. government agencies, including the Federal Trade Commission and the Department of the Treasury. In December, China was fingered for attacks that compromised Google last December but also targeted top government research firms, contractors, and think tanks.
Testifying before Congress in February, former national intelligence director Mike McConnell said the United States may be on the brink of an all-out cyberwar–one we are unprepared to fight.
“From the beginning the government’s approach to networks was to facilitate access,” says Richard Stiennon, chief research analyst for IT-Harvest and author of Surviving Cyber War. “Now that seems naïve. E-mail is its primary means of communications, and that’s completely exposed. Attackers from all over are having their way with government computer systems.”
The Fix: “Joe and Jane Citizen need to tell the federal government to comply with computer security standards published by the National Institute of Standards and Technology (NIST),” says Stiennon. “That will get us about 90 percent closer to where we need to be, so we can start focusing on the real bad guys.”
Google Could Rat You Out
How much does Google know about you? That depends on how much you rely on its cornucopia of free services. But that stored information may easily include the Websites you visit, the search terms you use, the maps you view, your contacts and calendar, your e-mail messages, your chat history, Google Voice phone records, YouTube videos and Picasa photos, the documents you store online, your blogs and advertising accounts, your status updates on Google Buzz, your location on Google Latitude, and–if you use an Android handset–all the data associated with your cell phone, too.
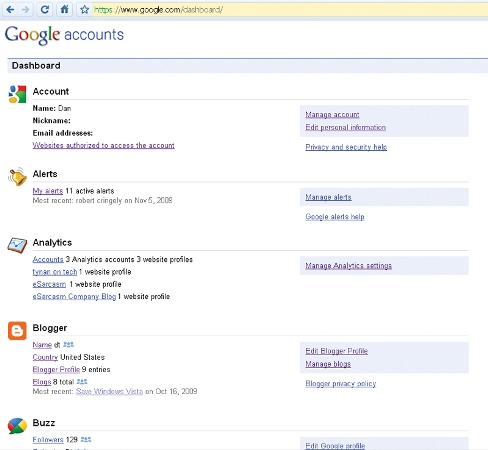
If the government comes knocking with a subpoena–or even just a strongly worded letter, per the Patriot Act–Google is obligated to hand everything over. Sure, the feds can get this data from anyone, but Google’s wealth of information (as well as its lengthy data-retention policies) makes their job much easier.
Even if you have nothing to hide from the authorities, all that stands between you and Christmas in July for an identity thief is your Gmail log-on and password; that’s the key that unlocks every other Google service. Last October, Google reported that thousands of Gmail accounts had been compromised by a phishing scheme that also targeted AOL, MSN Hotmail, and Yahoo. Even sophisticated users have had their Gmail accounts hijacked. Little wonder, then, that Chinese hackers targeted Gmail accounts when they compromised the service last December.
The Fix: Use Google Dashboard to see what information you’re sharing (prepare to be blown away), and adjust your settings accordingly. Make your Gmail password harder to guess, and change it every couple of months. If you think your Gmail account has been hacked or stolen, you may be able to use Google’s account-recovery page to get it back. And given Google’s recent stumbles over user privacy with Buzz, you might consider spreading the risk over different providers.
Pacemakers and Other Implants Can Be Hacked
Researchers at the University of Washington have demonstrated that medical implants that rely on wireless technologies for monitoring the devices and adjusting their settings are not secure.
In lab tests, scientists from UW, the University of Massachusetts Amherst, and Harvard Medical School were able to take control of a cardiac defibrillator and use it to induce ventricular fibrillation, a potentially lethal condition. They could also read sensitive medical information stored on the device and change it at will.
Study coauthor Tadayoshi Kohno, assistant professor at the University of Washington, says that similar techniques theoretically could be applied to other wireless medical devices, such as drug dispensers and neuro-stimulators.
“Medical devices are innovating at an extremely rapid pace,” says Kohno. “In the future they’ll be much more like full-grown computers. We did this study to raise awareness and increase our understanding of the security risks these devices could pose.”
The Fix: At present no fix exists, though the Food and Drug Administration and medical-device manufacturers are aware of the problem. There are no known cases of medical devices being hacked in the wild.
Even the study’s coauthor downplays the actual danger. “The risk to patients today is low,” adds Kohno. “These are amazing life-saving devices, and I would have no qualms about using one.”
Your PC May Be Killing You
Though electronics manufacturers have made great strides in reducing their use of harmful chemicals in recent years, tech gear still may contain brominated flame retardants–chemicals used to reduce the risk of fire that studies have linked to lower IQs in children and reduced fertility rates.
“BFRs used in the manufacture of circuit boards can be converted to highly toxic brominated dioxins and furans if the products are burned at the end of their life,” says Arlene Blum, executive director of the Green Science Policy Institute and a visiting professor of chemistry at UC Berkeley.
But even daily use can be dangerous, says Blum. “When used in plastic casings, BFRs can also migrate out of the plastic into the dust in the room and then enter the body via the hand-to-mouth contact.”
The Fix: While major manufacturers such as Apple, Dell, and HP have moved away from BFRs in recent years, certain products built before 2009–especially devices that generate a lot of heat, like laptops and laser printers–may still contain BFRs, says Michael Kirschner, associate director of the Green Science Policy Institute. “Do some research,” says Kirschner. “Almost all vendors now have an environmental section on their Websites that tells you about the materials they use.”
The news isn’t all bad, he adds. “Most manufacturers in the consumer arena have gotten the message to get additive BFRs out of their products.”
As for older products still in people’s homes? “They probably need to be replaced anyway, right?” Kirschner jokes.
Antivirus Software Won’t Protect You
Security programs won’t really protect you from the Internet’s worst nasties. “Antivirus software only catches the low-hanging fruit,” says Mark Kadritch, CEO of The Security Consortium and author of Endpoint Security. The increasing number of zero-day vulnerabilities–coupled with some vendors’ failure to fix security holes in their products for months or even years–means that even the most up-to-date antimalware products may still be behind the curve when it counts, he says.
The Fix: You can’t do without security software (see our Security Info Center for reviews of the latest security packages, plus how-tos and news), but to protect yourself more effectively you need to take extra steps such as saving your data to encrypted drives and installing VMware or other software that lets you create virtual machines and discard them as they become infected.
“At the end of the day, if you suspect your system has been compromised, blow it away and click ‘restore’ in VMware,” Kadritch says. “You may lose some e-mail, but you’ll get a brand-new system with the latest, greatest updates.”
Your Cell Phone Is a Homing Beacon
We’ll bet that you never leave home without your handset. Well, guess what: Wherever you roam, you can be found. You don’t even need a GPS chip in your phone–your using cell towers allows your provider to triangulate your position within a few hundred yards.
“Wherever you carry your phone, the government can go to your wireless provider and use those records to figure out where you are,” says the Electronic Frontier Foundation’s Jennifer Granick.
Of course, this information could save your life; cell phone tracking has assisted in locating kidnap victims and people stranded in the wilderness. But law enforcement has also used the technology to track people without probable cause. Documents obtained via a Freedom of Information Act lawsuit by the ACLU, the EFF, and the Center for Democracy and Technology reveal that the state of New Jersey obtained cell phone subscriber information 79 times between 2002 and 2008 without seeking a warrant.
Giving law enforcement free rein opens up broad opportunities for information gathering on people who aren’t even necessarily persons of interest in an investigation, says Granick.
“One example would be that police could find out the names of everyone who was near a political protest site just because they were investigating someone or something that happened there,” she says.
At press time, a federal appeals court was set to hear arguments in the New Jersey case. How the court rules may determine how much of a snoop your phone continues to be.
The Fix: If your handset has a GPS chip and you don’t want to be tracked, turn it off. Even then, the carrier may be able to ping your phone to determine the cell towers nearest you. Turning off your phone entirely is your best bet for dropping off the grid, if only temporarily. The next time you use your handset, though, you’ll be back on your carrier’s grid
.
A ‘Cheap’ Smartphone Is a Rip-Off
Your wireless company might like you to think that your handset is locked to one carrier for myriad technical reasons, but there’s really only one reason: profits. The carrier wants to lock you into paying hundreds of dollars a month for mobile voice and data service, and to accomplish that it will sell you a subsidized smartphone for much less than the company paid for it.
Spending more up front for an unsubsidized phone, however, might save you money in the long run. PCWorld contributing editor JR Raphael compared the fees for an unsubsidized $529 Nexus One phone (and an à la carte contract with T-Mobile) with those for the iPhone 3GS and the Motorola Droid, which are available only with a two-year contract (from AT&T and Verizon, respectively). The cost savings over two years: $1350, thanks largely to T-Mobile’s $80-per-month unlimited voice, text, and data plan (no contract required).
It gets better. Ben Ferguson, on his Nosugrefneb blog, compared a subsidized $295 Nexus One plus a two-year T-Mobile plan with an unsubsidized model using a $40 T-Mobile data plan and a $3-per-month VoIP account on Skype. Using the data plan and VoIP lopped an additional $482 off the cost–making that option $1800 cheaper than a subsidized iPhone.
The Fix: Do the math. As more vendors move toward an “open” handset model, paying more up front can save you a bundle in the long run.
Your Webcam May Be Watching You
Two-way video chat is fun. One-way chat–where you’re the one being watched–is not so much fun. But it’s more common than you might think.
In February, school officials in southeastern Pennsylvania found themselves in hot water after they installed software on school laptops that allowed them to activate students’ Webcams remotely. The school claimed that the software–which could snap a picture of whoever was using the MacBook at any time–was only for locating lost or stolen laptops. Outraged parents sued the district, and the story made international headlines.
Two weeks earlier, a woman reported being spied on via her Webcam by a Dell support technician, which she discovered when she realized the tech had turned on her Webcam without asking permission. Chinese cyberspy network GhostNet has reportedly taken over at least 1300 PCs worldwide, including the ability to operate their Webcams. In 2006, Spanish authorities arrested two teens after they hacked Webcams at a local college and tried to blackmail students caught in compromising situations. In 2004, an online intruder commandeered the computer of a 15-year-old girl in Houston, operating her Webcam remotely and typing messages on her screen about the clothes she was wearing.
The Fix: If you have an external Webcam, unplug it when you’re not using it. If your camera is built in, covering the lens with a sticky note should do the trick.
Your Boss Can (and Probably Does) Monitor Your Computer
Paranoia, schmaranoia. If you work in a medium-size or large organization, the folks in your IT department are keeping tabs on you.
Using software like Websense Triton or Barracuda Purewire, they can monitor the sites you visit, and scan the e-mail you send or receive. They can also check network-activity logs, or use software that captures your keystrokes or periodically grabs images off your screen.
According to the most recent surveys conducted by the American Management Association, two-thirds of all employers monitor employee Web and e-mail activity. About four out of ten use keyloggers or snoop around employees’ computer files. And one out of four firms has fired employees for Internet-related misdeeds.
Besides boosting productivity, companies are trying to avoid malware infestations, accidental leaks of confidential data, and liability for sexual-harassment suits if employees are exposed to Internet porn.
The problem? Selective enforcement, says Joe Rose, a labor-rights attorney based in Sacramento, California. Companies just collect the information and use it when needed to weed out troublemakers, complainers, or people who rub them the wrong way. “In my experience,” Rose says, “companies use this information selectively, either to pile on evidence in case of employee misconduct or if the employee engages in activity the company doesn’t like, such as labor organizing.”
The Fix: Don’t use company gear or networks to conduct personal business. If your employer gave you a BlackBerry, get your own cell phone, says Rose. Want to check your private Webmail account? Do it from your own computer and on your own network. In nearly all cases, your privacy rights at work are minimal at best.
You Can Fight the RIAA and Win
Organizations such as the Recording Industry Association of America and the Motion Picture Association of America can have your Website taken down simply by sending an e-mail to your host or Internet service provider–even if you’ve done nothing wrong. Under the endless gift to copyright holders known as the Digital Millennium Copyright Act, service providers may avoid liability by immediately removing material alleged to violate copyrights. They don’t require proof, and they don’t have to notify you in advance.
If your materials don’t infringe copyrights, however, you can file a DMCA counter-notification with your service provider. If the copyright holder doesn’t file suit against you within 14 days, your provider must restore what it deleted. (Of course, if the copyright holder calls your bet and files suit, you can withdraw your claim. Otherwise you’ll need to lawyer up, so pick your battles carefully.)
Unfortunately, service providers don’t always provide sufficient notice for site owners after the takedown; in some cases bloggers don’t even know which files to remove. Recently, six music bloggers had years’ worth of MP3 archives wiped from Blogger.com after Google received DMCA takedown notices from the International Federation of the Phonographic Industry. One site was reinstated, while a few others changed Web hosts; the rest were still dark as of this writing.
The Fix: Mail or fax your provider a counter-notification ASAP (e-mail isn’t an option). You’ll find a fill-in-the-blanks form at the Chilling Effects Clearinghouse site.
Your Passport Could Make You a Target for Crime-Wirelessly

Most American travelers are only dimly aware of a radio frequency ID chip embedded in the last page of their U.S. passport. The only indication as to the RFID chip’s presence is a small icon on the cover. The RFID chip permits a passport control officer to transfer the information on the passport’s “data page” wirelessly to a terminal, but security researchers have expressed concern that the range from which any RFID reader can pull data from a passport is far greater.
In 2006, security firm Flexilis demonstrated the ability to read RFID data at a range of several hundred feet, using a special antenna mounted to the stock of a sniper rifle (which the researchers used for both dramatic effect and ease of aiming). Last year, Chris Paget of the security firm IOActive drove around San Francisco and, within 20 minutes, copied all of the stored data right out of two unsuspecting U.S. passport holders’ pockets, using just a laptop plus off-the-shelf hardware and software costing a total of $250.
The Fix: “The privacy risks posed by RFID-enabled passports make dumpster diving for credit card slips look like child’s play,” says Andrew Brandt, lead threat research analyst for Webroot. “If a few hundred bucks’ worth of gear is all it takes to engage in mass identity theft, or to target citizens of a specific country for crime, it doesn’t seem too unreasonable to carry your travel documents wrapped up in aluminum foil.”
The Social Web Never Forgets
If you have an ugly encounter with someone in person, odds are you’ll both forget most of it within a week. Experience the same thing on the Internet, and it will be preserved forever. Worse, people have lost jobs, gotten sued, been arrested, or endured endless embarrassment due to things they said in e-mail or posted on Facebook.
“The Internet never forgets,” says the University of Washington’s Tadayoshi Kohno. “In the old days, if you wanted to make data disappear from your computer, you could take out your hard drive and take a sledgehammer to it. Today, much of our data is in the cloud. There’s no single hard drive to smash any more.”
The Fix: Kohno and other UW researchers have developed a technology called Vanish, which adds a “self-destruct” expiration mechanism to data shared across the Net. Vanish works by encrypting text and then distributing pieces of the encryption key across a dozen peer-to-peer networks. After a specified period of time, Vanish starts losing the keys, making the data unrecoverable. It can work with e-mail or with any text entered into a Web form, Kohno says. Though Vanish is still just a research project, curious users can download its open-source Firefox plug-in.
You Can Escape Almost Any Service Contract Without Penalties
You say you agreed to a two-year service contract to get a healthy discount on your broadband service or smartphone? You may be able to ditch your obligation without having to pay the usual early-termination fee–if your service provider has changed the terms on you in the time since you signed up.
Last December, Sprint sent a notice to its customers alerting them to a 40-cent monthly increase on all lines and a $5 increase on accounts with spending limits. That constituted a “materially adverse change of contract” per Sprint’s terms; this opened a porthole for unhappy Sprint customers to jump ship without incurring early-termination fees, which can amount to $150 or more. Similar changes in administration fees allowed T-Mobile users to switch last September and Verizon users to opt out in the spring of 2008.
The Fix: If your provider changes terms, and you decide to leave as a result, contact the company within the time period specified in your contract (usually 30 to 60 days). Make it clear that you’re switching because of the “materially adverse” nature of the change.
The NSA Is Tapping Your Data Stream
Remember all the hubbub about the Bush administration’s warrantless wiretapping? Nowadays, the National Security Agency still sifts through the petabytes of information traveling along the nation’s fiber backbone–but legally, thanks to some after-the-fact lawmaking by Congress.
Some quick background: In December 2005, the New York Times reported that the NSA had engaged in domestic digital surveillance without U.S. court approval. In January 2006, former AT&T technician Mark Klein provided documents to the Electronic Frontier Foundation confirming that the NSA had installed surveillance equipment at a major Internet hub in San Francisco.
In 2006 and 2008, the EFF filed suit against AT&T and the federal government, respectively, over warrantless wiretapping. Both suits were rebuffed by federal courts and are currently on appeal. In July 2008, Congress passed a bill granting retroactive immunity to telecoms for their participation in the NSA’s wiretaps.
“What people don’t know and should is that there is a dragnet sucking up all their communications so the government can review them,” says the EFF’s Jennifer Granick. “AT&T is still routing all of its data traffic through the NSA.”
The Fix: Short of pulling a Ted Kaczynski and holing up in a cabin in Montana, there isn’t much you can do. Last September, four Democratic senators introduced the Retroactive Immunity Appeal Act, which would make telecoms accountable for their role in warrantless spying, but the bill hasn’t gotten far. In the meantime, avoid googling “Osama” and “improvised explosive device” on the same day, unless you enjoy surprise visits from the Men in Black.
Your Facebook Apps Are Spying on You
Sure, it’s silly and fun to play Mafia Wars or to take one of the 2,345,678 quizzes on Facebook. When you install one of these apps, though, it gains access to any information you’ve designated as available to ‘Everyone’. Per Facebook’s Platform guidelines, this can include a huge amount of information, including your name, photo, birthday, location, job history, religion, political point of view, relationships, favorite books and movies, and so on. Much of this information is shared by default. It’s the motherload for data miners.
Facebook requires each app to adhere to your privacy preferences and to have its own privacy policy, but it doesn’t require apps to have a very good policy. Some, like Farmville’s policy, are fairly comprehensive; others appear to have been written by 12-year-olds.
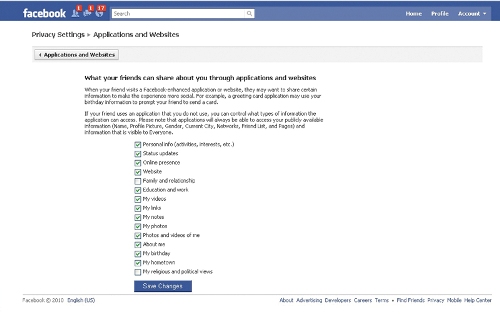
The Fix: Facebook recently introduced privacy controls that help limit what information apps can access. Use them. To start, log in and go to Account, Privacy Settings, Profile Information. Change any setting marked ‘Everyone’ to Only Friends or Friends of Friends. Then go to Applications and Websites, What your friends can share about you, and uncheck most if not all of the boxes.
Even then, there’s some information that Facebook simply won’t let you withhold, including your name, profile photo, friends, fan pages, and geographic location, plus the networks you belong to. So think twice before you start harvesting virtual crops or install “Lover of the Day.”
Your Geolocation Data Is Not Private
An army of marketers is looking to build profiles based on your habits and to sell you location-based services.
Telecommunications carriers maintain what is known as customer proprietary network information (CPNI), which can include details about your rate plans, who you called, and your location. By law, carriers can’t sell your CPNI without your permission, but how they obtain your approval can be quite sneaky. Often they’ll simply send an e-mail or letter giving you the opportunity to opt out; if you don’t respond, they’re free to sell your CPNI to whomever they please.
That doesn’t necessarily mean they do so right now. But as more phones become location aware and geocentric services become more widely used, the temptation may be overwhelming. The market for location data is expected to reach nearly $13 billion by 2014, according to Juniper Research.
A company that has your geographic data could sell it to stores and restaurants in your area or offer to pass sales promotions along to you on those businesses’ behalf. The classic example: You’re walking by a store when your phone receives a text message offering a 20 percent discount–but only if you go in and shop right now. Or you might get an e-mail saying, “We saw that you passed by our store the other day, and we want you to know that we’re having a sale.” As yet such scenarios are merely theoretical, but they’re highly creepy just the same.
The Fix: At this writing, Congress is holding hearings about geolocation data and privacy, which could result in new consumer safeguards (but don’t hold your breath). In the meantime, you can tell your carrier not to share your CPNI: Read the privacy policy on your provider’s Website and follow the steps required for opting out.
Illustrations by: Barry Blitt
When not polishing his tin-foil hat, Contributing Editor Dan Tynan tends his geek-humor empire at eSarcasm. Follow him on Twitter: @Tynan_on_tech.
Source: PC World




