Major security breaches in 2011 were perpetrated by hackers who broke into secured networks using entry points such as employee workstations and devices, data servers and public-facing Web site, according to a report by IBM X-Force.
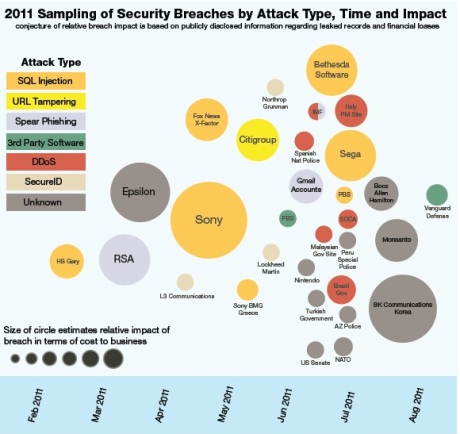
Big Blue’s hosted threat analysis service said that last year marked “The Year of the Security Breach” as 2011 saw an upsurge of attacks on companies such as Google, RSA, CitiGroup and Sony Playstation.
The IBM X-Force Mid-year Trend and Risk Report identified the most common entry points for attacks as:
- Public Web sites and data servers
- Employee workstations and devices
“Every page and script on every public facing website, as well as every other Internet facing service, is an opportunity for a motivated individual to find a hole,” the report stated. “The second point of entry is employee workstations or endpoints. Every employee with access on a corporate network is a potential target for an attacker.”
IBM warned that a company’s public facing Web site may contain thousands of script. The complexity of managing these can lead to the failure of identifying coding flaws that allow hackers to break through security.
A good way to deal with this is to implement a security policy that includes frequent and regular audit of Web codes and common injection points and the use of Web code scanning software.
Users are also common targets of attackers who use e-mail based social engineering tactics that persuade people to click on malicious links and messages. IBM advised that companies conduct regular employee security training and keep endpoints regularly patched up.